Is Wish Safe?
Wish is a global online marketplace that sets itself apart by offering massive discounts for shoppers. As you can imagine, it’s had its fair share of controversies throughout the years.
Some say it’s a fantastic place to restock their wardrobe, revamp their home or try out new accessories. Others will tell you to steer clear of it at all costs.
If something seems too good to be true, it usually is… or is it?
Let’s find out as we explore whether Wish is the answer for bargain-savvy shoppers or if its low prices are symbolic of poor quality and unreliable sellers.
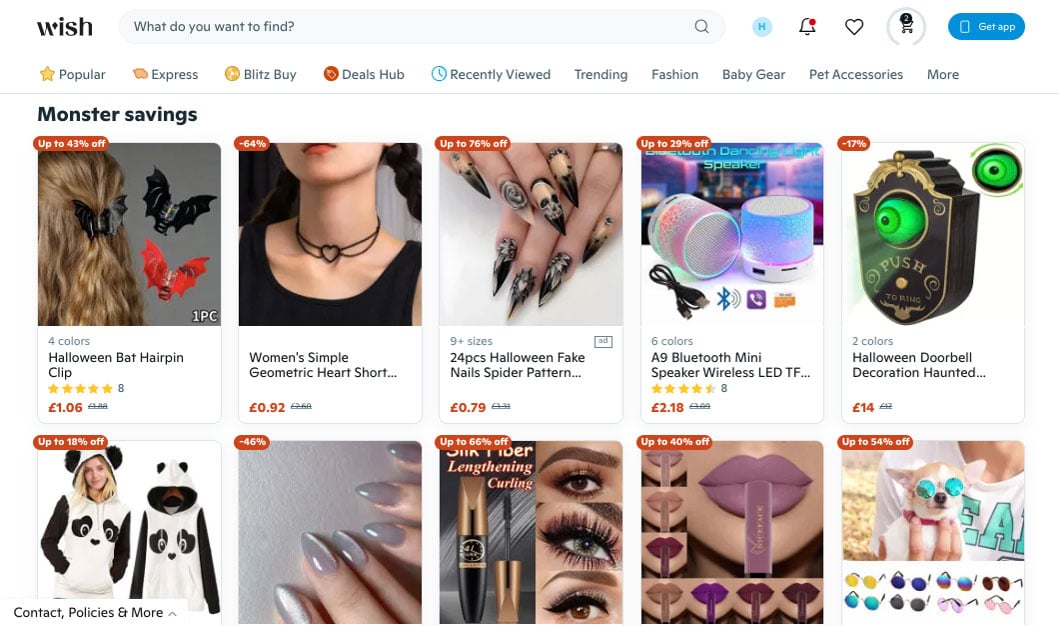
What is Wish?
Wish lets consumers buy cheap products from third-party sellers. Launched in 2010, the company’s business model is all about connecting buyers with manufacturers and sellers (mostly in China).
It has a huge presence, with millions of users in 60 countries filling up their baskets, but Wish isn’t as popular as it once was.
Head to the website or app, and you’ll find everything imaginable (and we mean everything). Think tech products, clothes, jewellery and pet products—all at a fraction of what you’d spend on Amazon or eBay.
Sure, the business model seems great, but is it all it’s cracked up to be? The platform serves as the middleman between you and the sellers. It facilitates transactions but has no control over product quality and shipping times.
Does Wish have security and privacy measures in place?
Online shopping will always come with some risks, but most platforms have security features that improve customer experience and reduce the risks of fraud. If you can’t resist some bargain buys, you’ll need to give Wish your name and email address when signing up.
The platform collects your location, browsing habits, and IP address but clearly states that this data personalises your shopping experience.
The Privacy Policy confirms that Wish uses your information only as needed and shares it with limited parties.
Other security features include:
- Two-Factor Authentication (2FA): Wish offers users a more secure experience by using 2FA. Once you attempt to sign in, the platform will send a code via email or phone to prevent unauthorised access.
- Strong Password Requirements: Wish encourages users to create strong, unique passwords that are difficult to guess.
- Secure Payment Processing: Secure payment gateways encrypt your information to protect it from unauthorised access. Even though these features are extra safeguards, you should still take steps to secure your online transactions when shopping online.
- Regular Security Audits: Wish conducts regular security audits to isolate and eliminate potential vulnerabilities.
Which payment methods does Wish accept?
You can access a variety of payment options on Wish, but it depends on your location. The most popular options are:
Credit/Debit Cards
You can use Visa, MasterCard and other major debit or credit card providers. The platform’s secure payment gateway will process these transactions, but that doesn’t mean they’re completely safe.
Scammers could access your credit card information and use it for fraudulent purposes, but you can keep yourself safe by learning how to spot credit card scams.
PayPal
PayPal needs no introduction. We all know it’s a convenient and safe payment method that offers more protection than your average debit card. Users also have added peace of mind through PayPal’s Buyer Protection Policy.
Despite PayPal’s benefits, failing to secure your account could increase its vulnerability. If someone hacks into it, they can use your payment information to make transactions.
Google Pay and Apple Pay
If you prefer mobile payments, Wish supports Google Pay and Apple Pay. Both methods are fast and secure, with biometric authentication for added protection.
Again, the main risk of digital wallets is that they’re connected to your phone. If you don’t activate your phone’s safety features and then lose it, your personal information is at risk.
Prepaid Virtual Cards
Prepaid virtual cards are a relatively new but innovative solution for making purchases online. Unlike other payment options, prepaid virtual cards don’t link to your bank account, providing extra security and anonymity.
With a Virtual Green Card, you can preload it with funds, make online transactions, and then reload it. A Virtual Black Card offers the most security, as you load it once and will order another card once the balance is depleted.
Klarna and Afterpay
Shoppers can also stock up on accessories, homeware and clothing items without paying anything in advance. The platform partners with BNPL companies like Klarna and Afterpay, enabling you to pay later or in instalments.
If you’re using Buy Now Pay Later, remember to secure your account and be on the lookout for unauthorised transactions.
Other potential risks of using Wish for online shopping
Wish may let you purchase affordable products, but it’s essential to be aware of the potential pitfalls of using the platform. They include issues with:
- Product Quality: Whether you’re buying clothing, accessories or anything else, always watch out for quality issues. The platform features sellers from all over the world, so the items you buy might seem great on the website but look nothing like the photos.
- Counterfeit Goods: Fake products are an ongoing issue on Wish, with incorrect product descriptions leading to unhappy customers. Remember, you’re not going to find genuine Nike apparel for €1, so let go of that wishful thinking.
- Shipping Issues: There will always be delays when you buy products from Wish. Most of these items ship from China, so waiting for a few weeks is normal. You can receive the items sooner if you’re willing to pay higher shipping costs.
- Security Risks: As of now, Wish hasn’t had any notable data breaches, but that doesn’t mean they won’t happen. The site’s legitimacy is genuine, but some users report cases of their accounts being breached by criminals.
How to stay safe and secure while shopping on Wish
As you can see, there are quite a few things to consider when deciding whether Wish is safe. There are definitely more secure platforms out there, and shopping with an EU retailer gives you more security, but those low prices might be too tempting to ignore.
If that’s the case, we recommend that you follow these safety tips to ensure your Wish experience doesn’t become a nightmare:
- Check For Honest Reviews: Before making a purchase, check reviews from previous buyers. If the seller’s consistently received positive reviews and customers upload photos of their products, you’ll better understand what you’re buying.
- Have Realistic Expectations: You can’t expect premium quality with a budget price tag, but there’s a difference between value for money and low-quality products. Be realistic and keep your expectations in check.
- Check Clothing Sizes: Now, this is a problem that plenty of Wish shoppers report, and it’s easy to see why. International sizing guides can be confusing, and it’s easy to order the wrong size. You can potentially avoid this by looking at views from other customers.
- Track Your Order: Even though the shipping times can be lengthy, tracking your order means you can receive support if the estimated delivery date passed. If you paid for faster shipping, you might be entitled to a refund.
- Persist With Customer Support: As the platform’s customer support is mostly automated, trying to get help from an actual person can be an uphill struggle. Wish has a Refund Policy, but taking photos and following the instructions can help you get your money back.
- Use secure payment methods: Always opt for secure payment methods like PayPal or prepaid virtual cards. If you decide to use your bank account, look for unauthorised charges and flag them immediately with your provider.
- Limit data sharing: Adjust your privacy settings within the Wish app, and avoid using social media logins to create your account. This reduces the amount of personal data you’re sharing with the platform.
The bottom line
Shopping on Wish can be safe if you take the necessary precautions, but it’s not without its risks. The platform offers great deals on a wide range of clothes, accessories and pretty much everything else you could imagine, but it’s not without faults.
Remember, when you’re paying excessively low prices, you can’t expect the best quality, but that doesn’t mean you should settle for faulty, counterfeit or inaccurate products.
By being a savvy shopper and exercising caution, you can mitigate many of the risks associated with shopping on Wish.
Shopping with a prepaid virtual card gives you peace of mind and a secure experience. These cards don’t link to your bank account and employ advanced security features. If you’re interested in leaving transaction worries behind, registering for a Getsby card takes just a couple of minutes.
Order your Virtual Cards online
Apply for a digital prepaid card online and receive the activation code via email within 2 minutes.